The DNS at Pi-hole, do just filter (domains and sub domains) .
The DNS at IPFire, do filter (domains, sub domains and also URL’s / site paths) by URL-Filter .
When clients (ex. an PC) requests resolving a domain to its IP at Pi-hole;
and get the IP of that requested domain reported by Pi-hole,
clients pass through IPFire either then, when Pi-hole resolves its outgoing DNS requests at the DNS of IPFire (in your case the eth green IP) .
Meant is : The URL-Filter of IPFire is useless … Clients reaches at this way not allowed URL’s, when an specific site path is not allowed .
Furthermore :
By using Pi-hole on eth green and blue, disturbs the LOG of Proxy at IPFire and you will not be able check every client communication and requested URL’s at IPFire Proxy-Logs .
The LOG will show just the IP of Pi-hole as a client, that requested a domain .
The right use of Pi-hole, were at eth red side, to resolve IPFire outgoing DNS requests, same idea as if you are using an external DNS service …
So you will be then able to use the benefits of both, of IPFire and of Pi-hole .
Make sure that clients be forced to use IPFire as the DNS and there the Proxy in none transparent too .
Needed links for configuration were added by Jon .
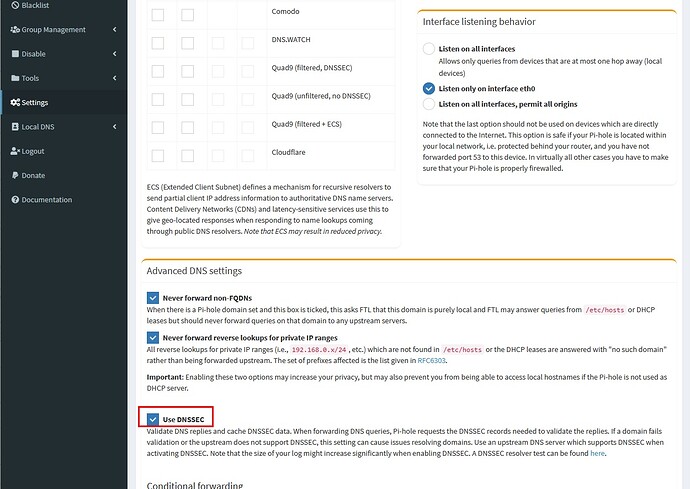
Now you can argue about DNSSEC and trusting DNS services, of your router, of your Pi-hole, of your ISP, of governments, of authority, of DoH, and of all others at Internet …
Whom you like to trust ??? No one !
By the way, I use two firewalls, where Pi-hole is behind the first one, and gets DNS resolved by first firewall .
Clients (DNS F-2) → Firewall-2 (DNS Pi) → L3-Switch + Pi (DNS F-1) + others → Firewall-1 (DNS external) → Router → external DNS
BR