Dear community,
I fiddled around with ipfire before (tested it on a Raspberry Pi 4B) and it worked pretty good, but now I wanted something proper! =) So I’ve been a proud owner of an IPFire Mini Appliance (including the Wireless Kit) for three days now (thanks again to Michael Tremer at this point for the fast, friendly and helpful contact :-)).
I’m still in the stage of testing / configuring and I wanted to share some observations and ask some questions.
Beforehand:
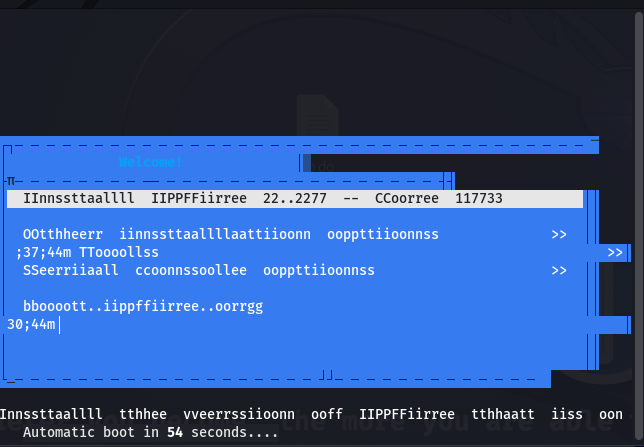
Clean installation via USB (mounted image on a Zalman/IODD) and the console-port worked like a charm, even though the boot-menu seemed a bit drunk. ![]()
I did a firmware-upgrade afterwards, so now it’s version 4.17.0.3 from August 2022. According to “pcengines”, 4.19.0.1 has been out recently, is there already a date when it will be available through pakfire?
My software-version itself is 2.27 - Core Update 173
So much for the facts, now to the observations / questions.
- Dongle
I have a Delock USB-to-ethernet-dongle plugged into the IPFire Mini Appliance (because I need a fifth Ethernet-Port). Everytime I reboot the appliance, the dongle is not shown in the zone-configuration (although it’s recognized by the device, because it’s listed via “lsusb”). But when I disconnect it from the running appliance and plug it back in again, then I can select a zone for it and it works without any problems.
Where could the error be? The problem appears on both USB-ports. How can I make ipfire recognize the dongle / show the dongle in the zone-configuration right from the start?
- Ping
Even when I grant full access from blue to green (just for testing), either for single IPs or the whole net, with all protocols and so on, I’m not able to ping a device in the green zone from the blue zone (or at least get no response to the ping), although I can connect to shared folders or web-services for example. Is this “works as designed” or am I missing out on something?
- Same old (long) story, but the last one for now, I promise!
 HT Caps and VHT Caps
HT Caps and VHT Caps
I opened up the IPFire Mini Appliance to make sure it has the Compex WLE600VX module (“lspci” just spit out “Qualcomm Atheros QCA986x/988x 802.11ac Wireless Network Adapter”).
I downloaded the instruction manual from Compex (nothing to find on Qualcomms website),
https://compex.com.sg/shop/wifi-module/802-11ac-wave-1/wle600vx-wifi5-11ac-qca9882-qca9892/
read through the ipfire-Wiki and forum and even picked some useful details from that teklager post about configuring IPFire Wifi
iw list gave out
Capabilities: 0x19ef
RX LDPC
HT20/HT40
SM Power Save disabled
RX HT20 SGI
RX HT40 SGI
TX STBC
RX STBC 1-stream
Max AMSDU length: 7935 bytes
DSSS/CCK HT40
Maximum RX AMPDU length 65535 bytes (exponent: 0x003)
Minimum RX AMPDU time spacing: 8 usec (0x06)
HT TX/RX MCS rate indexes supported: 0-15
VHT Capabilities (0x338001b2):
Max MPDU length: 11454
Supported Channel Width: neither 160 nor 80+80
RX LDPC
short GI (80 MHz)
TX STBC
RX antenna pattern consistency
TX antenna pattern consistency
So from “iw list”, the instruction manual, the teklager-posting and an intensive lecture of two different hostapd-example-configs, I figured, the right Caps for the Compex WLE600VX had to be
HT Caps: [OFDM][BPSK][QPSK][DBPSK][DQPSK][16-QAM][64-QAM][256-QAM][LDPC][HT20][HT40-][HT40+][SMPS-DYNAMIC][SHORT-GI-20][SHORT-GI-40][TX-STBC][RX-STBC1][MAX-AMSDU-7935][DSSS_CCK-40]
VHT Caps: [MAX-MPDU-11454][RXLDPC][SHORT-GI-80][TX-STBC-2BY1][RX-ANTENNA-PATTERN][TX-ANTENNA-PATTERN]
In “HT Caps” I set [SMPS-DYNAMIC] because even though “iw list” shows “SM Power Save disabled”, the instruction manual says this module supports “Spatial Multiplexing”. I choose [SMPS-DYNAMIC] over [SMPS-STATIC] because I considered it to be more efficient, but on the other hand I don’t know if it’s even working. ![]() Maybe someone could throw light on this. =)
Maybe someone could throw light on this. =)
Only on the teklagers site, I found that you also have to write down the modulations-caps ([OFDM][BPSK]…[256-QAM]). Oddly enough, the first time I activated WLanAP, I left them out and I could not get 802.11ac to work (only a,b,g,an or gn). Later, I punched them in and 802.11ac worked. Now, when I delete them from HT Caps, 802.11ac still works. Does anyone know why?
Both, my laptop and ipfire show a connection at around 800 Mbit/s (ipfire says it’s the maximum of 866, on my laptop it’s sometimes 575, sometimes 650, sometimes 780, whatever). Anyway some test-downloads from my NAS gave a maximum speed at about 45 mbyte/s, which would be 360 mbit/s. Is there any possibility to improve this? Maybe through other Caps? Considerations following:
On the Wiki-site for the Mini Appliance (no more than two links allowed for me :P) and the hardware-compatibility-list (no more than two links allowed for me :P) there are some more / different caps than the ones I have:
For “HT Caps”, there are additional [RX-STBC] and [SMPS-STATIC]. I guess [RX-STBC] is either wrong or obsolete, because according to hostapd it’s either [RX-STBC1], [RX-STBC12] or [RX-STBC123]. The thing about [SMPS-STATIC] I mentioned before.
For “VHT Caps”, there are additional [RX-STBC-1][MAX-A-MPDU-LEN-EXP7][BF-ANTENNA-2][SOUNDING-DIMENSION-2][VHT-LINK-ADAPT3] listed on the ipfire-pages, but I could not find any hints on these in the manual for the module nor via iw list. What are they for?
I read through Caps part on the openwrt-page (the only half-decent list I found) but my understanding in Wifi-technique is not that low level. Maybe again, someone could explain a few things. =)
For my understanding the “Caps” are just features, so it wouldn’t hurt to punch in as many as you can. If there are some completely false, the interface just would not come up, which is ok. But could there be some Caps that slow down the interface or lead to errors in the transmission?
I would really appreciate some answers / observations from you guys, so that we can get more facts down. I would like to correct / complete the two ipfire-Wiki-sites (because at the moment they are mutually contradictory), so that “new” people do not have to research as long as I did. =)
Hope, I didn’t bore you too much and looking forward to your answers. Have a nice weekend! ![]()
Greetings
Alex