Hi!
in addition of external blacklists/blocklists i need create my own blacklist with some internet IP adresses not listed in external blocklists, and store that file on ipfire locally. How can i achieve this and what rules or options i must create or enable in my ipfire configuration.
I don’t know of any easy way to add them.
But you can add them to a 'host group"
Thanks, i know that possibility, but is not as simple as edit one file and add one chekmark into config web page.
The unofficial IPFire plugin Banish would probably offer what you need, but it is not supported. I think it should work, as I remember it was updated to use libloc. However, you need to take care of installing it, update it and eventually fix problems.
Hi all,
would you mind to describe the non simplicity ? I use firewall.local for such things but not only IPTables, also IPSet as cfusco listed it might be worth to think about but it depends on what you want to do.
Best,
Erik
I want in my school with maximum possible simplicity block IPs who serves war games. Because most of them use https, it’s not possible achieve that with squid and/or urlfilter.
and how you gather the address information of the gaming server, how big is this list and how often you need to update this list ?
I monitor the websites (domains) visited by students when they play computer games. Then with nslookup or dig get appropriate IP addresses. I currently have a few dozen such IP’s
Am currently not sure why you do not try it with the firewall groups but if you want to stay on the console/SSH you can try it also with firewall.local and an blacklist.
If it is not a huge one (a few dozen) you can try it with a for loop and an separate blacklist. As an idea →
firewall.local
#!/bin/sh
# Used for private firewall rules
IPT="/sbin/iptables"
BLACKLIST="/etc/sysconfig/gamer_blacklist"
# See how we were called.
case "$1" in
start)
## add your 'start' rules here
# Block gamer blacklist
for i in $(cat ${BLACKLIST}); do
${IPT} -A CUSTOMFORWARD -d ${i} -j REJECT
${IPT} -A CUSTOMOUTPUT -d ${i} -j REJECT
done
;;
stop)
## add your 'stop' rules here
# Block gamer Blacklist
${IPT} -F CUSTOMFORWARD
${IPT} -F CUSTOMOUTPUT
;;
reload)
$0 stop
$0 start
## add your 'reload' rules here
;;
*)
echo "Usage: $0 {start|stop|reload}"
;;
esac
and a blacklist under e.g. ‘/etc/sysconfig/gamer_blacklist’ format should be one per line e.g.
135.148.137.xxx
23.227.170.xxx
208.167.243.xxx
192.223.29.xxx
94.23.156.xxx
74.91.124.xx
192.99.5.xx
74.91.125.xxx
31.133.1.xxx
after editing you can reload firewall.local with an
/etc/sysconfig/firewall.local reload
and your rules (every IP have an own rule entry) should be viewable under
iptables -L
with name resolution but also under WUI → Firewall → iptables, check under CUSTOMFORWARD and/or CUSTOMOUTPUT .
Also, an ping IP should deliver an ‘Destination Port Unreachable ping: sendmsg: Operation not permitted’ .
As a first idea.
Best,
Erik
P.S.: There is also another topic → Custom rule for ip blacklist firewall.local which is a little similar but do have also some other ideas.
Link to firewall.local wiki → www.ipfire.org - firewall.local
Thanks for the suggestion! I’m tried the firewall groups, but it seems quite laborious to me. Adding records to file and then restart service seems much more simpler.
You can use this script with local stored blacklist. If you have questions how to use i can help a bit…
Is there a particular need to have a “local” blocklist?
You could share the blocklist file on a local webserver, or anywhere else,
you can even use a pastebin type service:
Can’t get easier than this, right :))
Are you familiar with SSH?
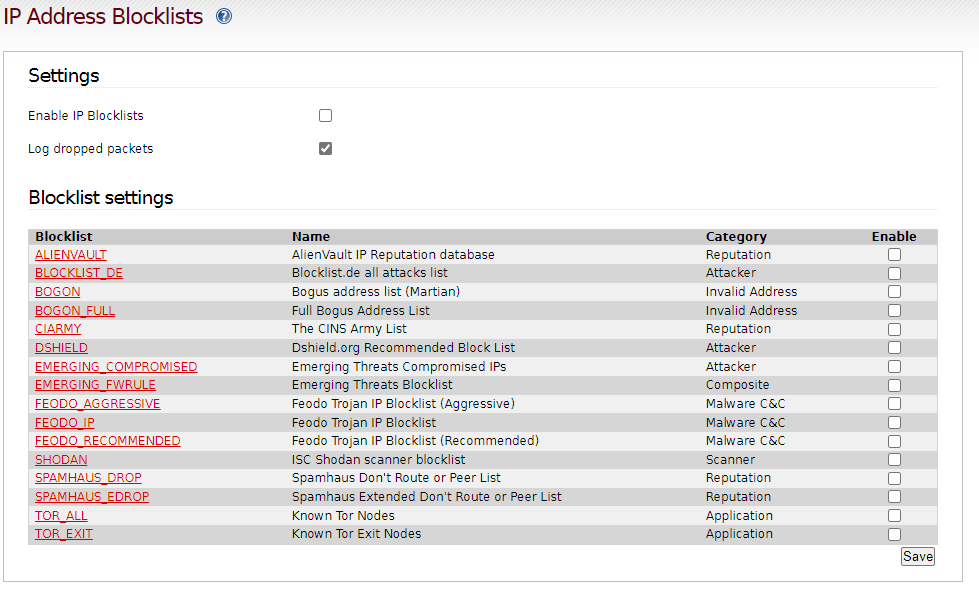
Just modify /var/ipfire/ipfireblocklist/sources
let me know the link to your blocklistfile and I can try to help
Wondering if a git acct. with a .txt file won’t do the job. If you have the domains in url filter and also Guardian addon also do ipblocking.
GIt acct is perfect for txt, you can also link to the RAW file, if you are having issues.
I’m familiar, but there all sources is from internet (http/https protocol). I need add local file from ipfire filesystem itself. What syntax for that?
Could you post some of your sources ?
IP blocklist usually just has IP addresses not necessarily http or https