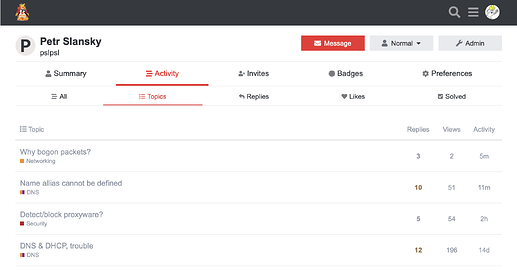
Continuing the discussion from Feature Request: Arpwatch add-on:
Article explaining arpwatch.
Video at YT, Arpwatch in pfSense, nice!
I think that author missed importance of file /var/lib/arpwatch/arp.dat, it is database of all MAC addresses ever visiting your network. My database had data for about 10 years. Format is like this:
# head -3 /var/lib/arpwatch/arp.dat
ec:b1:d7:42:af:6e 192.168.222.116 1687383245 elite eth0
90:1b:0e:1d:a8:83 192.168.222.1 1687383225 ipfire eth0
d8:50:e6:2f:a2:56 192.168.222.119 1687382381 vivo eth0
Other interesting feature is that it can detect “bogon” hosts in the network, like this one (/var/logs/syslog):
Jun 21 21:16:29 c4 arpwatch: new station 192.168.222.1 90:1b:0e:1d:a8:83 eth0
Jun 21 21:19:36 c4 arpwatch: new station 192.168.222.119 d8:50:e6:2f:a2:56 eth0
Jun 21 21:30:08 c4 arpwatch: bogon 213.28.29.235 90:1b:0e:1d:a8:83 eth0
Jun 21 21:45:08 c4 arpwatch: bogon 213.28.29.235 90:1b:0e:1d:a8:83 eth0
Jun 21 22:15:09 c4 arpwatch: message repeated 2 times: [ bogon 213.28.29.235 90:1b:0e:1d:a8:83 eth0]
Jun 21 22:30:09 c4 arpwatch: bogon 213.28.29.235 90:1b:0e:1d:a8:83 eth0
I am not sure why I see IP address 213.28.29.235 in my local network; that is IP address of my RED interface and MAC address is from ipfire gateway, so it looks like some problem with “ipfire” gateway, such packets should not be here…
I found a way to start arpwatch on Debian server. I ignore systemd configuration and I started it manually with “arpwatch -i eth0”; If file /var/lib/arpwatch/arp.dat doesn’t exists, it has to be created with touch /var/lib/arpwatch/arp.dat. This is just basic setup, no email alarms, just monitor network, report to syslog and update arp.dat file…
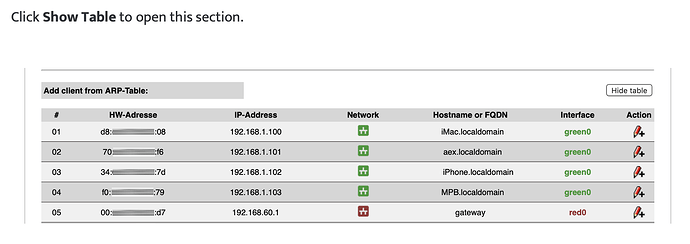
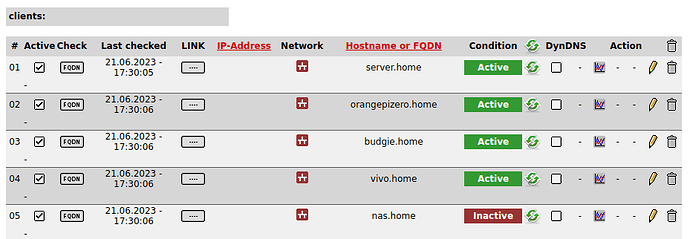
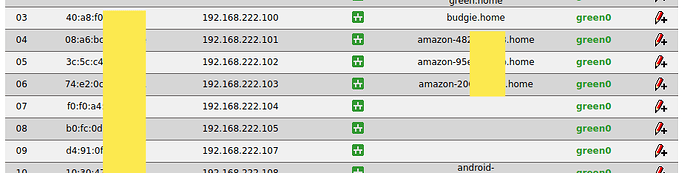
UPDATE. bogon packets I capture are ARP packets sent from ipfire to find “nas.home” that has IP address 192.168.222.22; this computer is down but it is configured in “wio” extension (who is online). I captured several packets with tcpdump and I see that four ARP queries were sent with interval 1 second and those had correct source IP address 192.168.222.1; after that one more ARP query is sent and this one has source IP address from RED, that is not expected. This happens every 15 minutes (refresh interval configured in WIO service configuration). I assume this is a bug in some Linux networking process responsible for ARP but it could be a feature, I am not sure. What about firewall rules at IPfire, shouldn’t be these packets captured and eliminated??
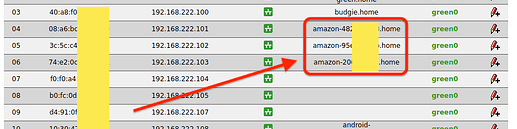
Screenshot from Wireshark, packets captured in GREEN network…