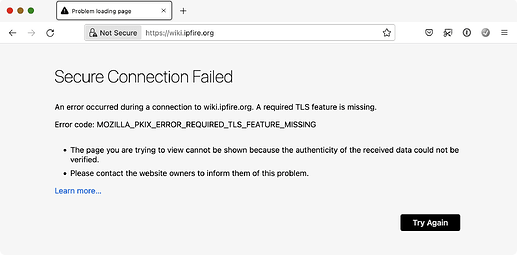
Suddenly I am getting MOZILLA_PKIX_ERROR_REQUIRED_TLS_FEATURE_MISSING from mozilla when I try a connection with https://wiki.ipfire.org, no problems with community www or blog. I can access normally the wiki with Safari or Brave.
Yes, me too, since ~ 3 hours.
I thought my Internet Security is the matter, but after research it is Mozilla.
All sites of IPFire works, just the wiki not.
BR
Trash
Here is the input from an IPFire Infrastructure email that was sent on this topic earlier today.
we currently have a glitch on https://wiki.ipfire.org/ : The TLS certificate
for this FQDN requires OCSP stapling - as pretty much all of the certificates
in our infrastructure do -, but the OCSP response from the web server is not
stapled.Thus, browsers are currently complaining - Firefox, for instance, by giving
the (not exactly helpful) error code MOZILLA_PKIX_ERROR_REQUIRED_TLS_FEATURE_MISSING.
So it is being worked on to get the OCSP stapling in the web server.
Not sure how long it will take but I am sure it will be done as quickly as possible.
The wiki is back up and running again.
for the people that are ignorant of what OCSP stapling is and yet are curious to know, this is the summary from GPT4:
OCSP stapling, also known as TLS Certificate Status Request extension, is a protocol that servers use to improve the performance and security of websites, specifically in terms of how they handle SSL/TLS certificates. It addresses the overhead problem associated with the client directly querying the Certificate Authority (CA) to check the revocation status of a certificate.
Here’s a basic, low-level overview of how OCSP stapling works:
- Certificate Retrieval: When a server is set up, it receives a digital certificate from a Certificate Authority (CA). This certificate verifies the server’s identity and contains information about the server’s public key.
- OCSP Request: Normally, after the server presents its certificate to a client (such as a web browser), the client then contacts the CA directly to check if the certificate is still valid (i.e., it hasn’t been revoked). But with OCSP stapling, instead of having each client do this, the server periodically queries the CA’s Online Certificate Status Protocol (OCSP) responder itself to get the current revocation status of its own certificates.
- Response Handling: The OCSP responder sends a status report back to the server. This report is time-stamped and signed by the CA.
- Stapling: The server “staples” this report to the certificate that it presents to clients. This is where the term “OCSP stapling” comes from.
- Client Verification: When a client connects to the server, the server sends both its certificate and the stapled OCSP response. The client can then verify the server’s certificate and its revocation status directly without needing to query the CA. It checks the timestamp and signature on the stapled OCSP response to make sure it’s valid and recent.
OCSP stapling benefits servers by reducing the number of queries they must make to the CA, thus improving performance. It also provides additional privacy for clients because the CA doesn’t see a record of which clients are checking the status of the server’s certificate.