Sorry I wasn’t saying all ports aren’t useful or that I was going to drop them… I know dns/voip and some other services are very useful being on specific ports.
In my situation I have very slow upload speed, and I just want my family to be able to enjoy slightly laggy netflix/youtube/etc without it affecting my job, where I use zoom all the time for meetings etc. Even at low quality it interrupts people talking and myself.
Until just recently this worked great, zoom was using udp ports 8801-8802 (I couldnt find any level 7 rules that worked), but now they switched to ssl 443 (and some random 50k ports), and I feel like this is a trend caused by the desire for security, but it ends up making the internet difficult to prioritize for those of us who really need to do that. Now youtube looks exactly like zoom, and I’m pretty much screwed. Personally I don’t need this security, and I believe it could have been done without using port 443 (there was another encryption option before this).
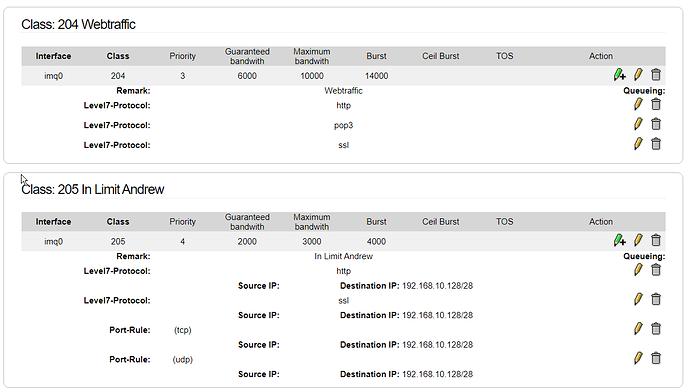
The only way I can see to prioritize my meetings now would be to create a set of IP’s for the endpoint ISP of the people I connect to (Bell/Rogers) and/or for the zoom servers and add my internal IP for upload shaping. I’ve set it up like below, but I haven’t managed to get it working yet for class 200:
class 102 voip:
tcp source: 192.168.1.X (me, static)
class 200 voip:
tcp source: 3.208.72.0/24 - ZOOM (usually I connect to these servers)
tcp source: 99.224.0.0/11 - ROGERS (most people I chat with are in this range)
Or I could try what the OP was doing and enable postrouting. Does anyone know if postrouting has other problems, aside from limiting local service traffic outbound?
Edit: Another option would be to add a level 7 protocol for netflix, or “D.A.S.H.” i think it’s called, then I could reverse-prioritize or something (put streaming below default like p2p). Does youtube still use rtsp?
Edit 2: How do I actually enable postrouting? I thought you just had to change a value in that file, but I dont see anything similar at all?