I made changes to /var/ipfire/proxy/advanced/acls/include.acl because I needed to implement access restrictions (using Squid) among various servers within the same BLUE network.
It should be noted that a I HAVE a SMART switch can block access between BLUE servers if Squid is not active.
# Opens access GREEN
acl rete_green src 10.168.1.0/16
http_access allow IPFire_green_network rete_green
# Urls allowed for image display of IPFire Squid
# 10.168.1.0/16 = GREEN
# 10.10.1.0/16 = BLU
# .254 = IPFire
acl special_url1 url_regex ipfire.localdomain:800/squid-internal-static/
http_access allow special_url1
acl special_url2 url_regex 10.168.1.254:800/squid-internal-static/
http_access allow special_url2
acl special_url3 url_regex 10.10.1.254:800/squid-internal-static/
http_access allow special_url3
# Urls allowed for wpad.dat
acl special_url4 url_regex http://10.10.1.254:81/wpad.dat
http_access allow special_url4
acl special_url5 url_regex http://10.168.1.254:81/wpad.dat
http_access allow special_url5
# deny to the IP client network access to IPFire
acl dominio2 dstdomain ipfire.localdomain
http_access deny dominio2
acl dominio3 dstdomain 10.168.1.254
http_access deny dominio3
acl dominio5 dstdomain 10.10.1.254
http_access deny dominio5
acl dominio6 dstdomain 10.10.1.253
http_access deny dominio6
acl dominio7 dstdomain 10.10.1.252
http_access deny dominio7
It is crucial to follow the RULES SETTING ORDER. If a rule is met, everything that follows is ignored, as this is the underlying logic.
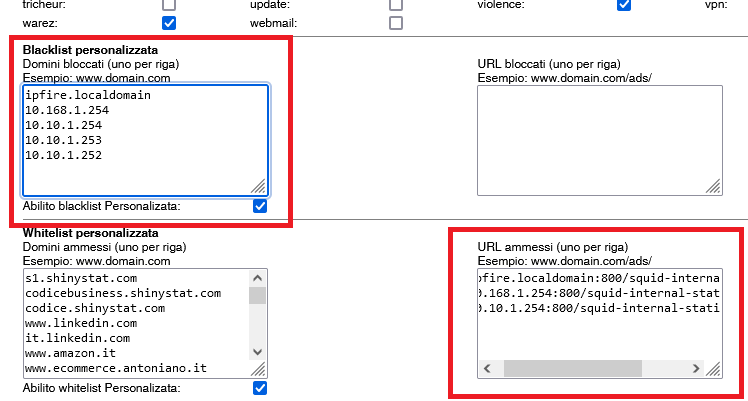
Alternatively, I have configured the same functionality through the graphical interface, as shown in the image. However, it’s important to note that if you disable URL filtering (keeping only the proxy active), the rules won’t be applied. This issue can be resolved by modifying “include.acl.”
Here is a reference image:
I have conducted numerous tests, and it appears that everything is working perfectly. I am open to any suggestions for improving the rules.
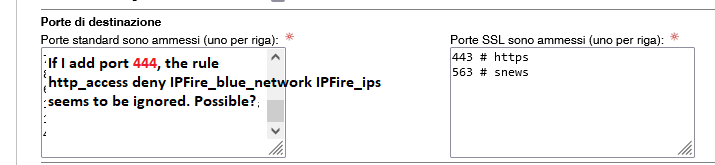
Additionally, I have noticed another issue, highlighted in the following image:
Thank you in advance for any advice, and have a great day.