I have done some testing out with OpenVPN client certificates that I have created in CU175 with OpenSSL-3.x
The certificates worked with no problems on my Linux laptop, both with Network Manager (with OpenVPN plugin installed) and also directly from the command line using the openvpn command.
My laptop has OpenSSL-3.1.1 and OpenVPN-2.6.4
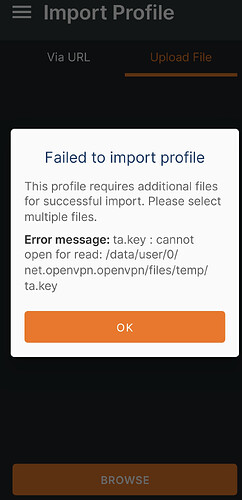
I then tried the certificates with my Android phone and found that trying to load the new certs into the Android Certificate Store failed with the error message that the password was incorrect. The same .p12 file was able to be opened up on my Linux Laptop so I am certain the password is correct. Without being able to upload the .p12 certs into the Android Certificate Store I can’t do any testing with the OpenVPN for Android and OpenVPN Connect apps.
I suspect that the Android 11 on my phone (last security update August 2022) is not able to read .p12 files created with Openssl-3.x for some reason.
Since Android version 8 they have used BoringSSL, the Google fork of OpenSSL. I have not been able to find out what version of BoringSSL is in Android 11 and the phone manufacturers don’t always follow all the updates done by Android. Even if I had the BoringSSL version number I am not sure I could find from that if it would correctly read .p12 files created with OpenSSL-3.x
So if you are using an Android Phone check with a newly created client certificate if it can be uploaded into the certificate store. If not then keep the old client certificate set.
Bear in mind that those older certificates will expire at some time as the default lifetime is 730 days.
My Android Phone client certificate will expire in November 2023. I have the feeling that the Android 11 software is not likely to get many more updates on my phone as Android 12 & 13 are out with 14 coming along before too soon. The phone may never be able to upload the newer, more secure, client certificates.
At that point I will probably stop using the phone for any OpenVPN RW activities and solely use my Linux Laptop.
EDIT:
The Linux gcr-viewer also does not like to open up the openssl-3.x .p12 files.
It complains of
gcr-viewer[18503]: unsupported or invalid mac: 2.16.840.1.101.3.4.2.1
That is a difference between the old and the new .p12 certificate containers. The old ones used a MAC of SHA1 while the new ones use a MAC of SHA256.
That is obviously okay for Openssl because I can still use openssl-1.1.1t to successfully open a .p12 file created with openssl-3.1.1
Does anyone on the forum use OpenVPN and have a phone or table with Android 12 or 13 to carry out the test of trying to upload a new certificate into the Android Certificate Store?