Hi Jon,
should we ever publish an IPFire handbook in a paperback version, “don’t panic” would be a great cover indeed - similar to The Hitchhikers Guide To The Galaxy. 
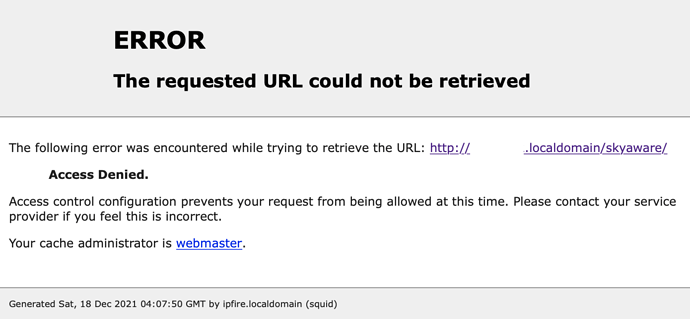
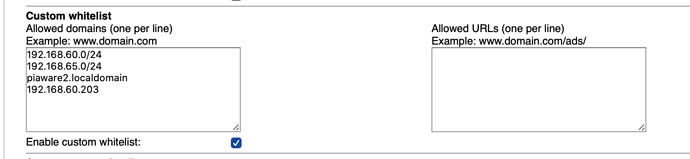
So, no, there is no need to panic, and this expected: The anomaly detection for selectively announced network basically triggers on any destination libloc does not find an Autonomous System to in the database currently present on the IPFire machine in question.
This includes IP space being not globally routable, such as RFC 1918 (192.168.0.0/16 et al.) - the idea behind this is people operating legitimate websites do host them on IP space that is globally announced. “Internal” sites, such as ipfire.localdomain, are some sort of collateral damage here. Sorry for causing confusion.
By the way: The ASNBL helper script, which performs both the Fast Flux detection and the detection for selectively announced networks, can be called interactively like this:
[root@maverick ~]# su -s /bin/bash squid
bash-5.1$ /usr/bin/asnbl-helper.py /var/ipfire/proxy/asnbl-helper.conf
Dec 16 22:18:49 squid-asnbl-helper[5101] WARN: No ASNBL configured. This is acceptable as long as this script is configured to do anything, you just have been warned...
Dec 16 22:18:49 squid-asnbl-helper[5101] INFO: ASN database operational - excellent. Waiting for input...
Changing to another user is necessary, since it won’t run as root for security reasons. Afterwards, you can query any FQDN or IP address, and it will result OK in case of a hit, and ERR if the destination is fine:
ipfire.org
ERR
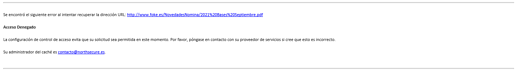
www.foke.es
Dec 16 22:19:11 squid-asnbl-helper[5101] WARN: Destination 'www.foke.es' resolves to IP addresses 'fe80::ccde:4cff:fea2:57ae' without corresponding ASN, probably selectively announced
Dec 16 22:19:11 squid-asnbl-helper[5101] INFO: Denying access to destination 'www.foke.es' due to suspected selective announcements
OK
rcacademy[.]at
Dec 16 22:19:14 squid-asnbl-helper[5101] WARN: Destination 'rcacademy[.]at' exceeds ASN diversity threshold (9 > 5), possibly Fast Flux: [3786, 6400, 8151, 8452, 9318, 12252, 13124, 35819, 38932]
Dec 16 22:19:14 squid-asnbl-helper[5101] INFO: Denying access to possible Fast Flux destination 'rcacademy[.]at'
OK
ipfire.org is begin, the next one is the FQDN Roberto had issues with, while rcacademy[.]at (brackets inserted for preventing accidental access) is a real-world example of a malware domain being hosted on a Fast Flux network. See also its VirusTotal result.
Perhaps this makes things more transparent. As always, feel free to play around with /usr/bin/asnbl-helper.py, and drop me a line in case of any questions or quirks. 
Thanks, and best regards,
Peter Müller
 ), since they cannot access this site at all.
), since they cannot access this site at all.