Hallo,
we’ve an old server standing in a corner … now we tested it - OK running
Is this machine usable to iPFire ?
inxi says:
Machine:
Type: Desktop Mobo: Supermicro model: X9SCI/X9SCA v: 0123456789
serial: 0123456789 BIOS: American Megatrends v: 2.3a date: 01/06/2021
CPU:
Topology: Quad Core model: Intel Xeon E31270 bits: 64 type: MCP
L2 cache: 8192 KiB
Speed: 2901 MHz min/max: 1600/3800 MHz Core speeds (MHz): 1: 2016 2: 1827
3: 1863 4: 1771
Memory:
RAM: total: 7.75 GiB used: 200.2 MiB (2.5%)
Array-1: capacity: 32 GiB slots: 4 EC: Single-bit ECC
max module size: 8 GiB note: est.
Device-1: DIMM_1A size: 2 GiB speed: 1333 MT/s type: DDR3
detail: synchronous bus width: 64 bits total: 128 bits
manufacturer: Micron part-no: 9JSF25672AZ-1G9K1 serial: FD9D0DB9
Device-2: DIMM_2A size: 2 GiB speed: 1333 MT/s type: DDR3
detail: synchronous bus width: 64 bits total: 128 bits
manufacturer: Micron part-no: 9KSF25672AZ-1G6K1 serial: 2978DB62
Device-3: DIMM_1B size: 2 GiB speed: 1333 MT/s type: DDR3
detail: synchronous bus width: 64 bits total: 128 bits
manufacturer: Micron part-no: 9JSF25672AZ-1G9K1 serial: 0D5709DB
Device-4: DIMM_2B size: 2 GiB speed: 1333 MT/s type: DDR3
detail: synchronous bus width: 64 bits total: 128 bits
manufacturer: Micron part-no: 9KSF25672AZ-1G6K1 serial: DEAB464B
Network:
Device-1: Intel 82574L Gigabit Network driver: e1000e
IF: enp2s0 state: down mac: 00:25:90:27:49:76
Device-2: Intel 82574L Gigabit Network driver: e1000e
IF: enp3s0 state: down mac: 00:25:90:27:49:77
Device-3: Intel 82574L Gigabit Network driver: e1000e
IF: enp4s0 state: up speed: 1000 Mbps duplex: full mac: 00:25:90:27:49:78
Device-4: Intel 82574L Gigabit Network driver: e1000e
IF: enp5s0 state: down mac: 00:25:90:27:49:79
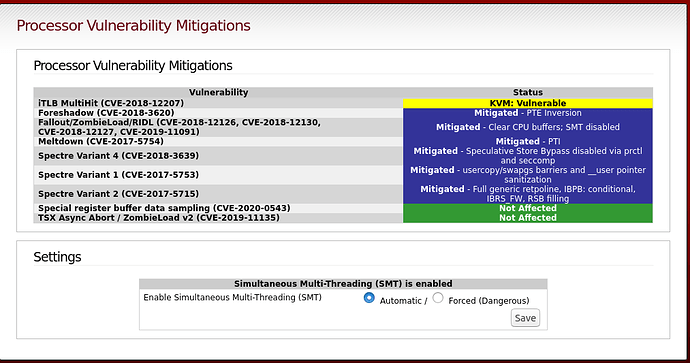
But there are some other problems and we don’t know is this a knockout ??
:~# grep . /sys/devices/system/cpu/vulnerabilities/*
/sys/devices/system/cpu/vulnerabilities/itlb_multihit:KVM: Mitigation: VMX unsupported
/sys/devices/system/cpu/vulnerabilities/l1tf:Mitigation: PTE Inversion
/sys/devices/system/cpu/vulnerabilities/mds:Mitigation: Clear CPU buffers; SMT disabled
/sys/devices/system/cpu/vulnerabilities/meltdown:Mitigation: PTI
/sys/devices/system/cpu/vulnerabilities/spec_store_bypass:Mitigation: Speculative Store Bypass disabled via prctl and seccomp
/sys/devices/system/cpu/vulnerabilities/spectre_v1:Mitigation: usercopy/swapgs barriers and __user pointer sanitization
/sys/devices/system/cpu/vulnerabilities/spectre_v2:Mitigation: Full generic retpoline, IBPB: conditional, IBRS_FW, RSB filling
/sys/devices/system/cpu/vulnerabilities/srbds:Not affected
/sys/devices/system/cpu/vulnerabilities/tsx_async_abort:Not affected
Thank you for every tip !