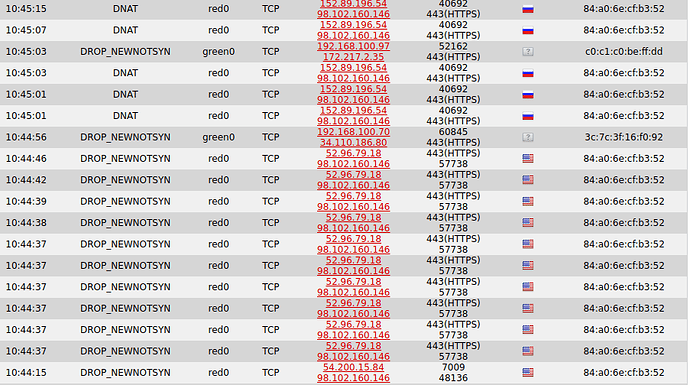
I have every country blocked except the US on my location block, but I still see inbound connections from other countries getting through when I look at my firewall logs. I am assuming it is being passed because it shows DNAT. A recent example from Russia is shown below (sorry for the weird file name, it is a screen shot). Am I missing something in my setup? Is there something weird with those IP addresses? Thanks and regards.
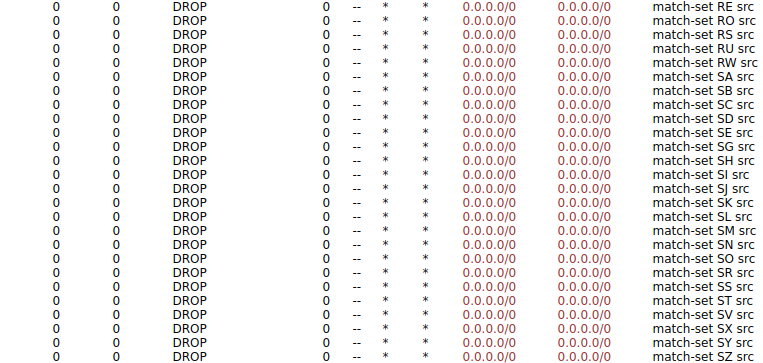
If you go in Firewall/IPTables and in the drop down menu you select LOCATIONBLOCK you should see the number of dropped packets and their origin. Do you see some of them coming from Russia?
EDIT: looking at the graphical representation of the Firewall routing, you can see that GEOIP block is also in the forward chain, where the DNAT should go. Maybe those logs are showing the DNAT packets that were delivered to that chain, before getting to the GEOIP block. Someone that understands IPTable hopefully will comment on this.
You could also look at the logs in the console using grep, searching for some of those IP. You should see them getting dropped.
I took a look at LOCATIONBLOCK in iptables, and it showed all zeros, for all countries that we are blocking. Does that mean zero is getting blocked or zero is getting through?
zero blocked.
Hello Jeff,
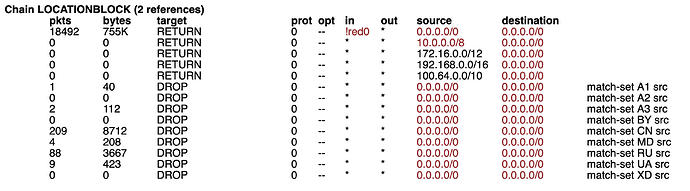
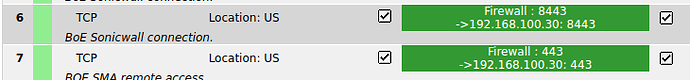
I assume you are trying to only allow access to your webserver on 443 from the US?
In this case you cannot use the generic Firewall->Location Block. You have to create a single DNAT firewall rule with the source: Location US and NAT to your internal servers IP with the desired port or modify your existing one.
Hope that helps.
Best regards,
-Stefan
Thanks, I will give that a try. I modified the firewall rules for those connections to Location: US. Before, they were set to RED. A follow up question then… If I need to set a firewall rule to limit access to a certain country, what does the Location Block do?
The Firewall->Location Block is a simple WUI feature to block incoming traffic from the selected countries, directly addressed to the RED interface (public address). Most time this feature is just used to reduce the amount of dropped and logged input traffic. ( Especially if you have a slow system or flash storrage…)
If any traffic hits a forwarded port it will be forwarded to the desired host because this is a completely different scenario. So to allow port forwarding only for certain amount of addresses or countries you have to select those or create groups and select them as your source.
See:
Best regards,
-Stefan
Sounds good. Thanks for the info. On a side note, activating the IP Address Blocklist is blocking a lot of incoming traffic (port scans, I think). We like that feature.