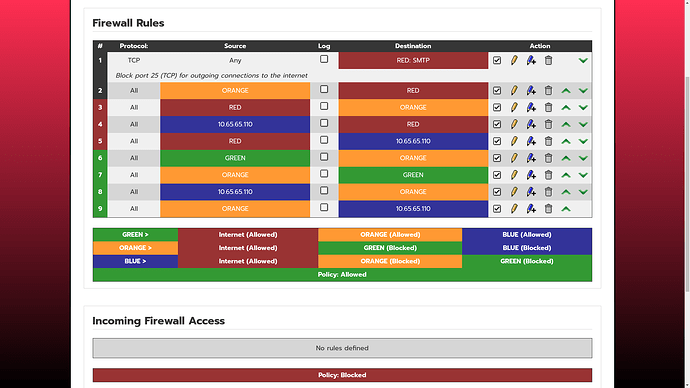
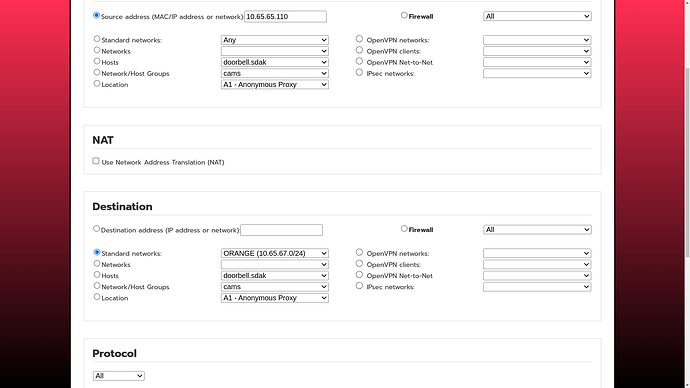
After the update to 189 I had to disable IPS on Orange as it suddenly blocked a Orange host to contact a MySQL database in Green through the defined firewall pinhole as I reported here: (CU189 - IPS enable / disable on Interfaces changed - #4 by robinr1)
Meanwhile I found that IPS indeed actively blocks that traffic as Potentially Bad Traffic:
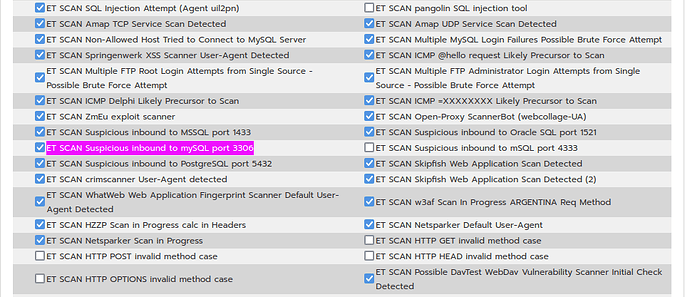
[Drop] [**] [1:2010937:3] ET SCAN Suspicious inbound to mySQL port 3306 [**] [Classification: Potentially Bad Traffic] [Priority: 2] {TCP} 192.168.2.2:58228 -> 192.168.0.9:3306
I’m not sure on how to prevent this from happening except disabling IPS completely on Orange. If anyone could guide me on this one, please do, I would like to have IPS enabled on Orange. You never know…
However, now after upgrading to 190, it became worse: suddenly Blue devices are no longer communicating over HTTPS with an Orange host despite a pinhole existing and no changes to the firewall. Connections now time out.
Again I have been searching long for the problem. When I restart the firewall (/etc/init.d/firewall restart) it works again, for some time. This can be for a few minutes up to half a day. And then it stops working again.
On a hunch, I have now tried disabling IPS on Blue, and suddenly it just works again, without explicit restarting of the firewall. So I did some digging in the IPS logging to check what rule would block Blue HTTPS to Orange. But I find no logging of it dropping those connections.
I have been live watching the IPS and firewall logging now, enable IPS on Blue, see HTTPS traffic timing out again, but nothing logged about it.
Disabling IPS on Blue again, and HTTPS traffic from Blue to Orange instantly works again.
I have this Orange HTTPS server also NATed over RED, and IPS is also active on RED ofcourse. But I have no problem contacting the Orange host from outside. The only difference between the RED rule and the Blue rule is that RED is using NAT and had SYN Flood protection ON.
Is anyone else experiencing similar problems or is able to simulate this problem in their end ?