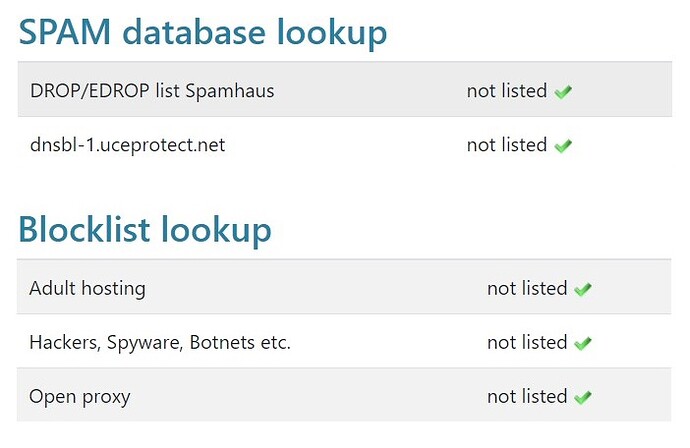
Firewall logs block a certain IP, I query this IP not listed in
DROP/EDROP list Spamhaus, is this a bug of IPFire?
In the wiki it says that these IP’s primarily come from Spamhaus DROP.
The full list is defined in the IPFire Location Database with special country code XD
https://wiki.ipfire.org/configuration/firewall/options#Drop packets from and to hostile networks
If you believe that the IP is not a Hostile Network then you should raise a bug about this giving the supporting data for your view.
Hi,
indeed, currently, Spamhaus DROP, EDROP and DROPv6 are solicited in addition to some ASNs and IP networks identified by the IPFire developers as rogue - that list can be retrieved here.
This is primarily because Spamhaus’ ASN-DROP list is still suspended from service due to “operational constraints”. Since it was very helpful, we tried to adapt the worst ASNs listed there, to protect IPFire users. Similar to Spamhaus’ policy, this of course strives for a zero false-positive rate, and we have not heard of FPs caused by this so far. ![]()
Could you post the IP address in question here? The corresponding /24 subnet is also sufficient.
Thanks, and best regards,
Peter Müller
The IP segment I want to access is American PEG TECH INC, ASN: 54600. It is a rental server business. It is possible that other customers have done harmful things before.
I think the Spamhaus DROP list is not up to date
I checked override-xd.txt and saw ISP and IP hijacker located in US this time, tampers with RIR data. drop: yes
Is it the ISP’s problem, or is the tenant doing something harmful?
Hi,
thanks for your reply.
Unfortunately, AS54600 has not ceased to provide connectivity or services to miscreants hijacking stolen AFRINIC IPv4 address ranges. Offending BGP announcements:
155.235.0[.]0/18163.197.192[.]0/18164.155.128[.]0/19165.3.0[.]0/17
These are all allocated to defunct African organizations, primarily in South Africa, have been stolen, and are now used by cyber criminals for malicious hosting. There is no way AS54600 / PEG TECH INC is not aware of this, given the plethora of news these incidents made, such as:
- https://mybroadband.co.za/news/security/367188-the-great-african-ip-address-heist-south-african-internet-resources-worth-r558-million-usurped-with-shady-domains.html
- The Great $50M African IP Address Heist – Krebs on Security
Therefore, AS54600 is considered to be tolerating malicious activity from its premises, which is why it is not recommended to process network connections from or to IP space propagated by this AS.
Please relocate your service to a different ISP.
Sorry to disappoint, and best regards,
Peter Müller
I understand the problem with the ASN 54600, I can’t decide to switch to another ISP.
Hope to add local exclusion list function, Just add my leased IP. I want to enable Drop packets from and to hostile networks