Hi,
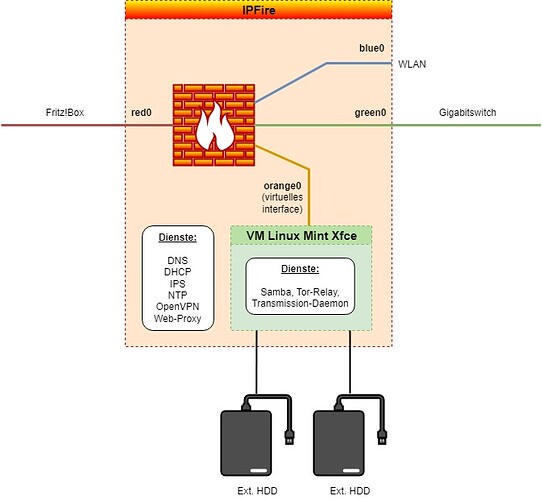
i am running a mint server with transmission-daemon and tor-relay under qemu in a virtual orange network.
When i activate the new firewall option “Pakete von und zu bösartigen Netzen (Spamhaus DROP-Listing, etc.) verwerfen”, i got thousands of dropped connections belonging to the transmission-daemon and the tor-relay in the firewall log.
How can i bypass the firewall for these connections from and to the mint server in orange?
Hi,
first, thank you for the detailed post - even with a graphic of the network. Excellent! ![]()
Running a Tor relay myself directly on IPFire, I also observe some DROP_HOSTILE events.
Apparently, there are a couple of Tor relays in such networks - in terms of anonymity, it might be an interesting discussion whether this is a good idea. Presumed the operators of such networks do not cooperate with law enforcement, this would be good for anonymity, but if there’s a phishing/malware/C&C server on every other IP address in that neighborhood, then it’s not wise to process traffic to the network in general. Oh well, the world is a complicated place… ![]()
The more straightforward approach would be not to bypass the “drop hostile” feature, but to disable it. Then, create a firewall rule dropping any traffic to the country XD (which is how we flag these networks), which will achieve mostly the same.
Mostly, because services provided by IPFire itself (such as IPsec and OpenVPN daemons) are not covered by that, since it traffic to them will be processed before any firewall rule configured via the GUI is considered. You could create a custom iptables rule in the firewall.local script, which could look like this:
iptables -A CUSTOMINPUT -i red0 -m geoip --source-country XD -j LOG_DROP
That being written, I think don’t really think any legitimate traffic originates from these “hostile” networks. People placing legitimate servers there should just complain to the ISP, urging them do get delisted from Spamhaus DROP.
Hope to have helped.
Thanks, and best regards,
Peter Müller
Hi,
thankyou for your quick answer. I will do as you suggested ![]()
Best regards, Heiko