Hello guys
there are problems with a customer working in three locations.
Main location: OVPN server with various Roadwarrior connections (accessible via TCP 1194) and two n2n connections (each accessible on TCP 1195 and TCP 1197)
A firewall rule for HTTPS on web / mail server in the green network.
At the external locations: OVPNClient connect to the main location at the respective connections / port
For a week (after updating from Core approx. 127 to Core 151) there has been the phenomenon that the n2n connections no longer want to be established automatically after daily forced disconnection by the provider.
All locations can be reached via DDNS. This still works correctly.
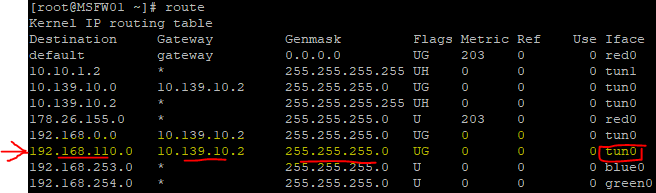
My guess is a routing problem. But I don’t know which side.
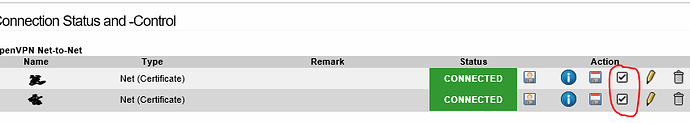
To get it running for the day, I have to uncheck the connection between client and server and then set it again.
What do I have to do to get this working again?
Server side:
09:18:43 YYYn2n[16979]: MANAGEMENT: TCP Socket listening on [AF_INET]127.0.0.1:1197
09:18:43 YYYn2n[16979]: NOTE: the current --script-security setting may allow this configuration to call user-defined scripts
09:18:43 YYYn2n[16979]: Diffie-Hellman initialized with 4096 bit key
09:18:43 YYYn2n[16979]: WARNING: normally if you use --mssfix and/or --fragment, you should also set --t un-mtu 1500 (currently it is 1400)
09:18:43 YYYn2n[16979]: ROUTE_GATEWAY 192.168.2.1/255.255.255.0 IFACE=red0 HWADDR=00:0d:b9:4e:eb:e5
09:18:43 YYYn2n[16979]: TUN/TAP device tun1 opened
09:18:43 YYYn2n[16979]: TUN/TAP TX queue length set to 100
09:18:43 YYYn2n[16979]: /sbin/ip link set dev tun1 up mtu 1400
09:18:43 YYYn2n[16979]: /sbin/ip addr add dev tun1 local 10.9.8.1 peer 10.9.8.2
09:18:43 YYYn2n[16979]: /etc/init.d/static-routes start tun1 1400 1503 10.9.8.1 10.9.8.2 init
09:18:43 YYYn2n[16979]: /sbin/ip route add 192.168.10.0/24 via 10.9.8.2
09:18:43 YYYn2n[16979]: TCP/UDP: Preserving recently used remote address: [AF_INET]88.88.88.88:1197
09:18:43 YYYn2n[16979]: Socket Buffers: R=[87380->87380] S=[16384->16384]
09:18:43 YYYn2n[16979]: Listening for incoming TCP connection on [AF_INET]192.168.2.254:1197
09:18:46 YYYn2n[16979]: MANAGEMENT: Client connected from [AF_INET]127.0.0.1:1197
09:18:46 YYYn2n[16979]: MANAGEMENT: CMD 'state'
09:18:46 YYYn2n[16979]: MANAGEMENT: Client disconnected
09:18:46 ZZZn2n[6455]: MANAGEMENT: Client connected from [AF_INET]127.0.0.1:1195
09:18:46 ZZZn2n[6455]: MANAGEMENT: CMD 'state'
09:18:46 ZZZn2n[6455]: MANAGEMENT: Client disconnected
09:20:16 YYYn2n[16979]: TCP connection established with [AF_INET]88.88.88.88:1197
09:20:16 YYYn2n[16979]: TCP_SERVER link local (bound): [AF_INET]192.168.2.254:1197
09:20:16 YYYn2n[16979]: TCP_SERVER link remote: [AF_INET]88.88.88.88:1197
09:20:16 YYYn2n[16979]: GID set to nobody
09:20:16 YYYn2n[16979]: UID set to nobody
09:20:16 YYYn2n[16979]: TLS: Initial packet from [AF_INET]88.88.88.88:1197, sid=5b0036dc 4b714e5c
09:20:16 YYYn2n[16979]: VERIFY OK: depth=0, C=DE, ST=Schleswig-Holstein, O=Customer, CN=YYY
09:20:16 YYYn2n[16979]: Outgoing Data Channel: Cipher 'AES-256-CBC' initialized with 256 bit key
09:20:16 YYYn2n[16979]: Outgoing Data Channel: Using 512 bit message hash 'SHA512' for HMAC authenticati on
09:20:16 YYYn2n[16979]: Incoming Data Channel: Cipher 'AES-256-CBC' initialized with 256 bit key
09:20:16 YYYn2n[16979]: Incoming Data Channel: Using 512 bit message hash 'SHA512' for HMAC authenticati on
09:20:17 YYYn2n[16979]: Control Channel: TLSv1.3, cipher TLSv1.3 TLS_AES_256_GCM_SHA384, 2048 bit RSA
09:20:17 YYYn2n[16979]: [IZ] Peer Connection Initiated with [AF_INET]88.88.88.88:1197
09:20:18 YYYn2n[16979]: WARNING: this configuration may cache passwords in memory -- use the auth-nocach e option to prevent this
09:20:18 YYYn2n[16979]: Initialization Sequence Completed
09:21:55 YYYn2n[16979]: Connection reset, restarting [0]
09:21:55 YYYn2n[16979]: SIGUSR1[soft,connection-reset] received, process restarting
09:21:55 YYYn2n[16979]: Restart pause, 1 second(s)
09:21:56 YYYn2n[16979]: NOTE: the current --script-security setting may allow this configuration to call user-defined scripts
09:21:56 YYYn2n[16979]: WARNING: normally if you use --mssfix and/or --fragment, you should also set --t un-mtu 1500 (currently it is 1400)
09:21:56 YYYn2n[16979]: Preserving previous TUN/TAP instance: tun1
09:21:56 YYYn2n[16979]: TCP/UDP: Preserving recently used remote address: [AF_INET]88.88.88.88:1197
09:21:56 YYYn2n[16979]: Socket Buffers: R=[87380->87380] S=[16384->16384]
09:21:56 YYYn2n[16979]: Listening for incoming TCP connection on [AF_INET]192.168.2.254:1197
09:22:12 YYYn2n[16979]: TCP connection established with [AF_INET]88.88.88.88:1197
09:22:12 YYYn2n[16979]: TCP_SERVER link local (bound): [AF_INET]192.168.2.254:1197
09:22:12 YYYn2n[16979]: TCP_SERVER link remote: [AF_INET]88.88.88.88:1197
09:22:12 YYYn2n[16979]: TLS: Initial packet from [AF_INET]88.88.88.88:1197, sid=a4b8ef99 d2f98c8a
09:22:12 YYYn2n[16979]: VERIFY OK: depth=0, C=DE, ST=Schleswig-Holstein, O=Customer, CN=YYY
09:22:12 YYYn2n[16979]: Outgoing Data Channel: Cipher 'AES-256-CBC' initialized with 256 bit key
09:22:12 YYYn2n[16979]: Outgoing Data Channel: Using 512 bit message hash 'SHA512' for HMAC authenticati on
09:22:12 YYYn2n[16979]: Incoming Data Channel: Cipher 'AES-256-CBC' initialized with 256 bit key
09:22:12 YYYn2n[16979]: Incoming Data Channel: Using 512 bit message hash 'SHA512' for HMAC authenticati on
09:22:12 YYYn2n[16979]: Control Channel: TLSv1.3, cipher TLSv1.3 TLS_AES_256_GCM_SHA384, 2048 bit RSA
09:22:12 YYYn2n[16979]: [IZ] Peer Connection Initiated with [AF_INET]88.88.88.88:1197
09:22:13 YYYn2n[16979]: Initialization Sequence Completed
09:22:31 YYYn2n[16979]: MANAGEMENT: Client connected from [AF_INET]127.0.0.1:1197
09:22:31 YYYn2n[16979]: MANAGEMENT: CMD 'state'
09:22:31 YYYn2n[16979]: MANAGEMENT: Client disconnected
09:22:31 ZZZn2n[6455]: MANAGEMENT: Client connected from [AF_INET]127.0.0.1:1195
09:22:31 ZZZn2n[6455]: MANAGEMENT: CMD 'state'
09:22:31 ZZZn2n[6455]: MANAGEMENT: Client disconnected
09:22:56 YYYn2n[16979]: MANAGEMENT: Client connected from [AF_INET]127.0.0.1:1197
09:22:56 YYYn2n[16979]: MANAGEMENT: CMD 'state'
09:22:56 YYYn2n[16979]: MANAGEMENT: Client disconnected
09:22:56 ZZZn2n[6455]: MANAGEMENT: Client connected from [AF_INET]127.0.0.1:1195
09:22:56 ZZZn2n[6455]: MANAGEMENT: CMD 'state'
09:22:56 ZZZn2n[6455]: MANAGEMENT: Client disconnected
09:23:09 YYYn2n[16979]: MANAGEMENT: Client connected from [AF_INET]127.0.0.1:1197
09:23:09 YYYn2n[16979]: MANAGEMENT: CMD 'state'
09:23:09 YYYn2n[16979]: MANAGEMENT: Client disconnected
Client side:
09:16:40 YYYn2n[25687]: MANAGEMENT: Client connected from [AF_INET]127.0.0.1:1197
09:16:40 YYYn2n[25687]: MANAGEMENT: CMD 'state'
09:16:40 YYYn2n[25687]: MANAGEMENT: Client disconnected
09:17:42 YYYn2n[25687]: WARNING: normally if you use --mssfix and/or --fragment, you should also set --t un-mtu 1500 (currently it is 1400)
09:17:42 YYYn2n[25687]: Preserving previous TUN/TAP instance: tun1
09:17:42 YYYn2n[25687]: TCP/UDP: Preserving recently used remote address: [AF_INET]99.99.99.99:1197
09:17:42 YYYn2n[25687]: Socket Buffers: R=[87380->87380] S=[16384->16384]
09:17:42 YYYn2n[25687]: Attempting to establish TCP connection with [AF_INET]99.99.99.99:1197 [nonblo ck]
09:17:43 YYYn2n[25687]: TCP connection established with [AF_INET]99.99.99.99:1197
09:17:43 YYYn2n[25687]: TCP_CLIENT link local (bound): [AF_INET]192.168.178.254:1197
09:17:43 YYYn2n[25687]: TCP_CLIENT link remote: [AF_INET]99.99.99.99:1197
09:17:43 YYYn2n[25687]: Connection reset, restarting [0]
09:17:43 YYYn2n[25687]: SIGUSR1[soft,connection-reset] received, process restarting
09:17:43 YYYn2n[25687]: Restart pause, 160 second(s)
09:18:48 YYYn2n[25687]: MANAGEMENT: Client connected from [AF_INET]127.0.0.1:1197
09:18:48 YYYn2n[25687]: MANAGEMENT: CMD 'state'
09:18:48 YYYn2n[25687]: MANAGEMENT: Client disconnected
09:20:23 YYYn2n[25687]: WARNING: normally if you use --mssfix and/or --fragment, you should also set --t un-mtu 1500 (currently it is 1400)
09:20:23 YYYn2n[25687]: Preserving previous TUN/TAP instance: tun1
09:20:23 YYYn2n[25687]: TCP/UDP: Preserving recently used remote address: [AF_INET]99.99.99.99:1197
09:20:23 YYYn2n[25687]: Socket Buffers: R=[87380->87380] S=[16384->16384]
09:20:23 YYYn2n[25687]: Attempting to establish TCP connection with [AF_INET]99.99.99.99:1197 [nonblo ck]
09:20:24 YYYn2n[25687]: TCP connection established with [AF_INET]99.99.99.99:1197
09:20:24 YYYn2n[25687]: TCP_CLIENT link local (bound): [AF_INET]192.168.178.254:1197
09:20:24 YYYn2n[25687]: TCP_CLIENT link remote: [AF_INET]99.99.99.99:1197
09:20:24 YYYn2n[25687]: TLS: Initial packet from [AF_INET]99.99.99.99:1197, sid=f89551ae 76e32c0c
09:20:24 YYYn2n[25687]: VERIFY KU OK
09:20:24 YYYn2n[25687]: Validating certificate extended key usage
09:20:24 YYYn2n[25687]: ++ Certificate has EKU (str) TLS Web Server Authentication, expects TLS Web Serv er Authentication
09:20:24 YYYn2n[25687]: VERIFY EKU OK
09:20:24 YYYn2n[25687]: VERIFY OK: depth=0, C=DE, ST=Schleswig-Holstein, O=Customer, CN=ZZZ.dyndns.org
09:20:24 YYYn2n[25687]: Outgoing Data Channel: Cipher 'AES-256-CBC' initialized with 256 bit key
09:20:24 YYYn2n[25687]: Outgoing Data Channel: Using 512 bit message hash 'SHA512' for HMAC authenticati on
09:20:24 YYYn2n[25687]: Incoming Data Channel: Cipher 'AES-256-CBC' initialized with 256 bit key
09:20:24 YYYn2n[25687]: Incoming Data Channel: Using 512 bit message hash 'SHA512' for HMAC authenticati on
09:20:24 YYYn2n[25687]: Control Channel: TLSv1.3, cipher TLSv1.3 TLS_AES_256_GCM_SHA384, 2048 bit RSA
09:20:24 YYYn2n[25687]: [mart-hei.dyndns.org] Peer Connection Initiated with [AF_INET]99.99.99.99:119 7
09:20:25 YYYn2n[25687]: WARNING: this configuration may cache passwords in memory -- use the auth-nocach e option to prevent this
09:20:25 YYYn2n[25687]: Initialization Sequence Completed
09:22:02 YYYn2n[25687]: event_wait : Interrupted system call (code=4)
09:22:02 YYYn2n[25687]: /sbin/ip route del 192.168.100.0/24
09:22:02 YYYn2n[25687]: ERROR: Linux route delete command failed: external program exited with error sta tus: 2
09:22:02 YYYn2n[25687]: Closing TUN/TAP interface
09:22:02 YYYn2n[25687]: /sbin/ip addr del dev tun1 local 10.9.8.2 peer 10.9.8.1
09:22:02 YYYn2n[25687]: Linux ip addr del failed: external program exited with error status: 2
09:22:02 YYYn2n[25687]: SIGTERM[hard,] received, process exiting
09:22:19 YYYn2n[29044]: disabling NCP mode (--ncp-disable) because not in P2MP client or server mode
09:22:19 YYYn2n[29044]: WARNING: Using --management on a TCP port WITHOUT passwords is STRONGLY discoura ged and considered insecure
09:22:19 YYYn2n[29044]: OpenVPN 2.4.9 x86_64-pc-linux-gnu [SSL (OpenSSL)] [LZO] [LZ4] [EPOLL] [MH/PKTINF O] [AEAD] built on Jun 26 2020
09:22:19 YYYn2n[29044]: library versions: OpenSSL 1.1.1h 22 Sep 2020, LZO 2.09
09:22:19 YYYn2n[29045]: MANAGEMENT: TCP Socket listening on [AF_INET]127.0.0.1:1197
09:22:19 YYYn2n[29045]: WARNING: normally if you use --mssfix and/or --fragment, you should also set --t un-mtu 1500 (currently it is 1400)
09:22:19 YYYn2n[29045]: ROUTE_GATEWAY 192.168.178.1/255.255.255.0 IFACE=red0 HWADDR=00:0d:b9:4e:ef:79
09:22:19 YYYn2n[29045]: TUN/TAP device tun1 opened
09:22:19 YYYn2n[29045]: TUN/TAP TX queue length set to 100
09:22:19 YYYn2n[29045]: /sbin/ip link set dev tun1 up mtu 1400
09:22:19 YYYn2n[29045]: /sbin/ip addr add dev tun1 local 10.9.8.2 peer 10.9.8.1
09:22:19 YYYn2n[29045]: /sbin/ip route add 192.168.100.0/24 via 10.9.8.1
09:22:19 YYYn2n[29045]: TCP/UDP: Preserving recently used remote address: [AF_INET]99.99.99.99:1197
09:22:19 YYYn2n[29045]: Socket Buffers: R=[87380->87380] S=[16384->16384]
09:22:19 YYYn2n[29045]: Attempting to establish TCP connection with [AF_INET]99.99.99.99:1197 [nonblo ck]
09:22:20 YYYn2n[29045]: TCP connection established with [AF_INET]99.99.99.99:1197
09:22:20 YYYn2n[29045]: TCP_CLIENT link local (bound): [AF_INET]192.168.178.254:1197
09:22:20 YYYn2n[29045]: TCP_CLIENT link remote: [AF_INET]99.99.99.99:1197
09:22:20 YYYn2n[29045]: GID set to nobody
09:22:20 YYYn2n[29045]: UID set to nobody
09:22:20 YYYn2n[29045]: TLS: Initial packet from [AF_INET]99.99.99.99:1197, sid=955df1e0 d537e13d
09:22:20 YYYn2n[29045]: VERIFY KU OK
09:22:20 YYYn2n[29045]: Validating certificate extended key usage
09:22:20 YYYn2n[29045]: ++ Certificate has EKU (str) TLS Web Server Authentication, expects TLS Web Serv er Authentication
09:22:20 YYYn2n[29045]: VERIFY EKU OK
09:22:20 YYYn2n[29045]: VERIFY OK: depth=0, C=DE, ST=Schleswig-Holstein, O=Customer, CN=ZZZ.dyndns.org
09:22:20 YYYn2n[29045]: Outgoing Data Channel: Cipher 'AES-256-CBC' initialized with 256 bit key
09:22:20 YYYn2n[29045]: Outgoing Data Channel: Using 512 bit message hash 'SHA512' for HMAC authenticati on
09:22:20 YYYn2n[29045]: Incoming Data Channel: Cipher 'AES-256-CBC' initialized with 256 bit key
09:22:20 YYYn2n[29045]: Incoming Data Channel: Using 512 bit message hash 'SHA512' for HMAC authenticati on
09:22:20 YYYn2n[29045]: Control Channel: TLSv1.3, cipher TLSv1.3 TLS_AES_256_GCM_SHA384, 2048 bit RSA
09:22:20 YYYn2n[29045]: [mart-hei.dyndns.org] Peer Connection Initiated with [AF_INET]99.99.99.99:119 7
09:22:21 YYYn2n[29045]: WARNING: this configuration may cache passwords in memory -- use the auth-nocach e option to prevent this
09:22:21 YYYn2n[29045]: Initialization Sequence Completed
09:22:21 YYYn2n[29045]: MANAGEMENT: Client connected from [AF_INET]127.0.0.1:1197
09:22:21 YYYn2n[29045]: MANAGEMENT: CMD 'state'
09:22:21 YYYn2n[29045]: MANAGEMENT: Client disconnected
09:23:35 YYYn2n[29045]: MANAGEMENT: Client connected from [AF_INET]127.0.0.1:1197
09:23:35 YYYn2n[29045]: MANAGEMENT: CMD 'state'
09:23:35 YYYn2n[29045]: MANAGEMENT: Client disconnected