@hvacguy
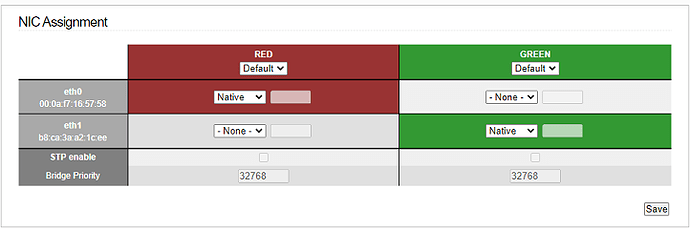
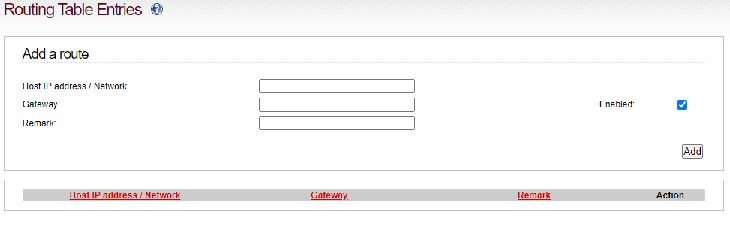
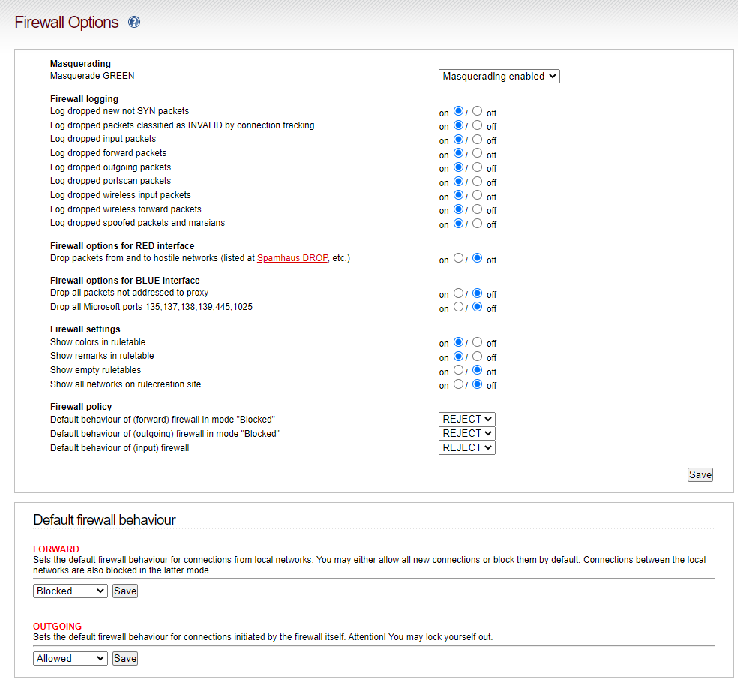
Clearly not doing what I need ![]() . I’m trying to prevent all access from Red network to Green Network, but do allow ModbusTCP traffic (on port 502) through from Green to Red, and then any replies from Red to Green. Should also allow ping requests from Green to Red and back. Other than that, nothing.
. I’m trying to prevent all access from Red network to Green Network, but do allow ModbusTCP traffic (on port 502) through from Green to Red, and then any replies from Red to Green. Should also allow ping requests from Green to Red and back. Other than that, nothing.
@bbitsch
I did see that article, and figured things should just work but they are not. In my attempt at getting it to work, it’s entirely possible I changed a setting that shouldn’t be. Here’s a list of settings that, to me, appear to be set correctly but perhaps my understanding of the associated help pages is wrong and thus the setting is incorrect…?